 The CRTC has served its first-ever warrant, after the Canadian government’s anti-spam legislation (CASL) came into effect in July 2014, to take down a Toronto-based malware server.
The CRTC has served its first-ever warrant, after the Canadian government’s anti-spam legislation (CASL) came into effect in July 2014, to take down a Toronto-based malware server.
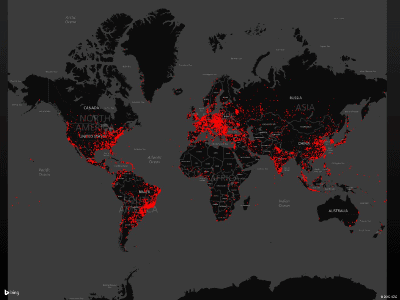
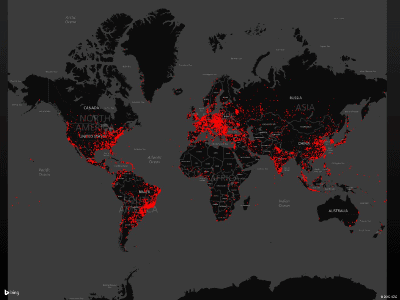
The server, which had been acting as a command-and-control point for distributing Win32/Dorkbot malware, a family of computer worms responsible for infecting upward of a million computers in 190 countries, capable of creating a botnet that can leverage a network of infected computers to attack a particular server with a distributed denial of service attack (DDoS).
The warrant was approved by a judge of the Ontario Court of Justice, and was executed by an international team led by the RCMP in collaboration with the FBI, Europol, Interpol, Public Safety Canada, the Canadian Cyber Incident Response Centre, security vendor ESET, the Computer Emergency Response Team Polska, the Department of Homeland Security’s U.S. Computer Emergency Readiness Team, and Microsoft.
“We are pleased to work alongside our partners during this investigation to mitigate the harm caused to Canadians and citizens in other countries by Dorkbot,” said CRTC Chief Compliance and Enforcement Officer Manon Bombardier. “These are very egregious botnets that are used for illicit activities and can lead to identity theft and fraud. This operation shows that partnerships between domestic and international law enforcement agencies are key in the fight against transnational cyber threats. I am grateful the RCMP provided assistance in this matter.”
Dorkbot, which was first seen in 2011, can be spread through USB flash drives, instant messaging programs and social networks.
Infected computers can then join a botnet, stealing passwords, downloading and installing malware, and engaging in DDoS attacks.
In a blog post, Microsoft said that it began noticing that Dorkbot was attempting to hijack login details for people’s Facebook, Gmail, Netflix, PayPal and Twitter accounts.
While this is a first victory for Canada’s anti-spam legislation, people can continue to send tips to the Spam Reporting Centre, which forwards its information to the CRTC, the Competition Bureau and the Office of the Privacy Commissioner, who are responsible for enforcing CASL.
The key issue around the CRTC’s anti-spam law revolves around the idea of “consent”, and its two varieties: “express” and “implied” consent. Express consent is someone actively saying, “Yes, I want you to send me these emails.”
Implied consent needs an existing relationship in which the recipient hasn’t expressly agreed to receive a communication from you but has opened the door a crack, such as if they’ve purchased something or if they’ve downloaded a trial version of your software or given you a business card at a trade show, for example.
In order to upgrade that business card relationship from “implied” to “express” consent status, though, it will be the sender’s responsibility to send a confirmation email asking, “Is it all right if I start sending you marketing emails?” in order to stay legally clean.
A sender must also always provide an “unsubscribe” opt-out in every subsequent email sent.
Bottom line, if called upon by the authorities, “you need to be able to provide proof of opt-in for every address on your list.”
Leave a Reply
You must be logged in to post a comment.




 Share
Share Tweet
Tweet Share
Share




Comment