Ontario court says no to U.S. seizure of Megaupload servers
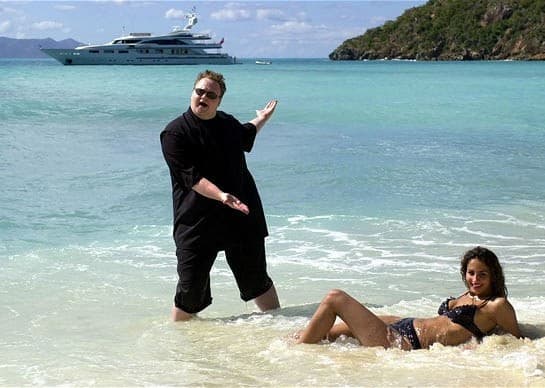
Megaupload founder Kim Dotcom’s New Zealand mansion was raided by the US Department of Justice last January 19th. It was about a year ago today that girthy hacker and rogue entrepreneur Kim Dotcom (whose mother calls him Kim Schmitz), the founder of Megaupload, was getting Kim Kardashian type media exposure after the US Department of Justice launched an international case against him.
The US government alleged that Megaupload had generated “more than $175 million in criminal proceeds and (caused) more than half a billion dollars in harm to copyright owners.”
Dotcom, along with three others named in the suit were arrested on January 19th, 2012 in New Zealand.
The US Government’s warrants extended to nine countries, and it went to court for the right to seize Megaupload servers located in Ontario. Last week, an Ontario court rejected the request for the servers, or mirror images of them.
Documents for the case of Canada (United States of America) v. Equinix Inc., 2013 ONSC 193 (CanLII) said that
“…there is an enormous volume of information on the servers and that sending mirror image copies of all of this data would be overly broad, particularly in light of the scantiness of the evidence connecting these servers to the crimes alleged by the American prosecutors.”
The court cited the 2011 case of R. v. Jones 2011 ONCA 632 in which it “rejected the notion that authority to search a computer gave unfettered access to all data there located”
“This is not because the warrant should be struck as “too broad”, in the sense that it contained no limitations on the ability of the police to search the computer, and therefore improperly invaded the high expectation of privacy the respondent had in the contents of his computer, as the respondent argues. It is because the warrant itself is properly restricted in the circumstances. Although it contained no limitations on the types of files that could be examined, it was reasonably focused and limited in the types of evidence the police could seek; and that evidence did not include evidence of child pornography.”
Megaupload, which was founded in 2005 was shuttered with the US Government’s actions last year. The shutdown of Megaupload led to widespread DNS attacks on various US Government websites.
There’s a great debate brewing on the matter at Michael Geist’s excellent blog here.
______________________
Nick Waddell
Founder of Cantech Letter
Cantech Letter founder and editor Nick Waddell has lived in five Canadian provinces and is proud of his country's often overlooked contributions to the world of science and technology. Waddell takes a regular shift on the Canadian media circuit, making appearances on CTV, CBC and BNN, and contributing to publications such as Canadian Business and Business Insider.
