 Security expert Lee Cocking says the blockchain technology used to secure Bitcoin transactions has “far reaching impacts on security and technology for our future“, and could be used to provide a new level of security for mobile devices.[/caption]
Security expert Lee Cocking says the blockchain technology used to secure Bitcoin transactions has “far reaching impacts on security and technology for our future“, and could be used to provide a new level of security for mobile devices.[/caption]
Technology made famous by Bitcoin could help BlackBerry win at mobile security, says one expert.
Lee Cocking, a former BlackBerry employee who left the firm with several others for Fixmo, which was recently acquired by Good Technology, has a new gig. Cocking is VP of Product Strategy at Guardtime, a Estonia-based cyber-security firm.
Cocking says a mobile device world that is increasingly characterized by a glaring lack of security could be transformed with the employment of the blockchain technology made famous by crypto-currency Bitcoin.
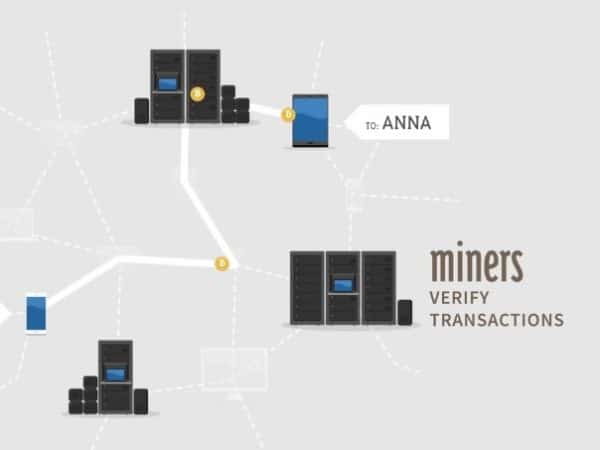
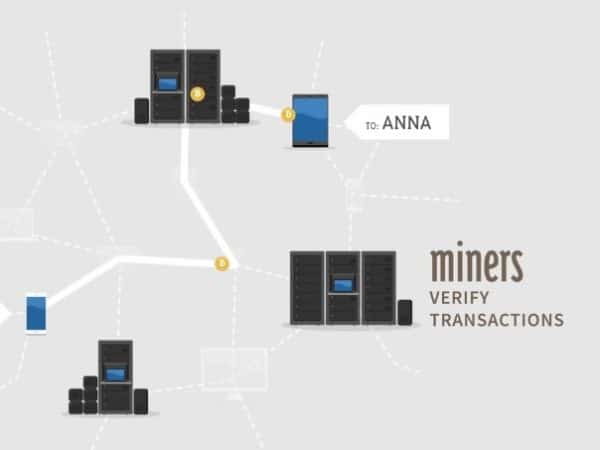
Blockchain technology secures transactions in the Bitcoin system by broadcasting a public ledger that records transactions. The maintenance of this ledger relies not on a single authority, but on the distributed architecture of a network that verifies transactions several times an hour. Once a transaction is verified, it is added to an updated ledger.
“The thing is,” says Cocking, “blockchains have far reaching impacts on security and technology for our future”.
“What if we could apply blockchain technology to mobile security?” he asks. “What if every mobile device, email, file transfer or firmware update is entered into the blockchain and can be independently and mathematically verified? All of a sudden their usefulness does not end as a distributed cash system, but rather emerges as a new way for the industry to prove the integrity of their data, the integrity of their transactions, and add a level of transparency to security that has been wildly lacking in our era of “trust-us” solution providers.”
Cocking says BlackBerry is especially qualified to use blockchain technology because it has always had a high regard for security, and its users buy the company’s devices in part because of the industry leading encryption they boast. He says he joined Guardtime because the company is dedicated to solving what he thinks is the Holy Grail of mobile technology.
“The missing piece to the mobile security puzzle I was struggling with was the ability to provide true integrity to mobile security, from the ground up,” he says. “The ability to not say “Trust me”, but actually allow third-party independent verification of the security system and every transaction that has occurred.”
During his year-long tenure at BlackBerry, CEO John Chen has constantly reiterated that the company must focus on core competencies, not the least of which is its hard earned reputation in security. In an interview with the Wall Street Journal to promote the BlackBerry Passport, Chen said the issue was of growing importance considering the environment of high-profile security breaches.
BlackBerry security currently works by using complex encryption to scramble messages between the device and a BlackBerry server. All BlackBerry traffic runs through the company’s own secure Network Operations Centers and is encrypted at each transfer point. The company says its solution was “purposefully designed” so that it can’t accommodate requests for a customer’s encryption key because it never possesses a copy of the key.
Apple, meanwhile, does not route its traffic through operations centres. Instead, it uses a form of security called Secure Sockets Layer, or SSL. SSL is a protocol that enables a device to confirm an identity between a browser and server. But this solution, explains Gizmodo’s Brian Barrett, has proven especially susceptible to “Man in the Middle” attacks, a form of high tech snooping that can intercept all communication on a shared network.
Cocking suggest bugs that pop up from time to time in Apple and in Andoid devices are not temporary inconveniences, they are inherent problems of a weaker security architecture.
“There’s a growing sense of urgency in the marketplace as Apple and Android solutions continue to run into security issues, he says, “and it’s creating a gap for BlackBerry to re-emerge as an innovative leader in secure mobility.”
Below: Bitcoin’s architecture explained in 5 minutes…
Comment
Leave a Reply
You must be logged in to post a comment.




 Share
Share Tweet
Tweet Share
Share




Apple have big problem, bendgate and gaygate.
Emails stored on external servers are not secure. Binfer is a great way to send secure email. It does not store emails anywhere so is very secure. The link is http://www.binfer.com.